It's not about monitoring, it's about productivity & compliance.
Here at Tech Success, we pride ourselves on being ahead of our competitors when it comes to new technology. We look to always enable our clients with innovative solutions that meet their objectives.
One of our clients was facing a challenge which was, ensuring continued compliance with PCI-DS as it pertains to the handling of credit card data. More specifically, the firm came to us requesting a technology that would be able to monitor employee activity to assist with:
- Identifying workflow involving credit card data.
- Is able to Enforce strict rules in terms of handling and storage or credit cards data in the appropriate systems.
- Is able to garner and gain forensic evidence of all credit card handling activity - in the event of non-compliance.
- Whilst ensuring best practices by identifying and preventing any non-compliant handling of credit card data.
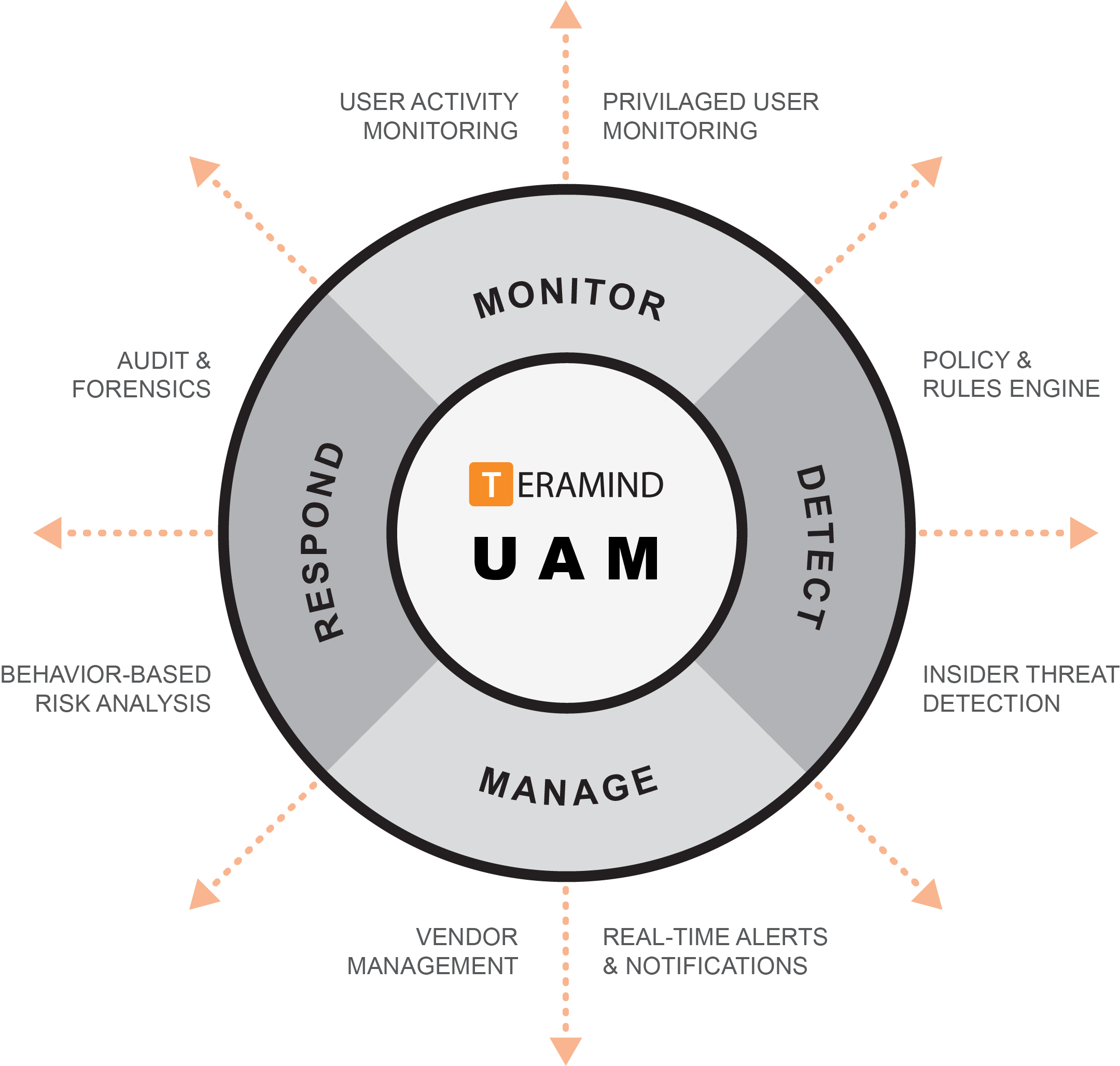
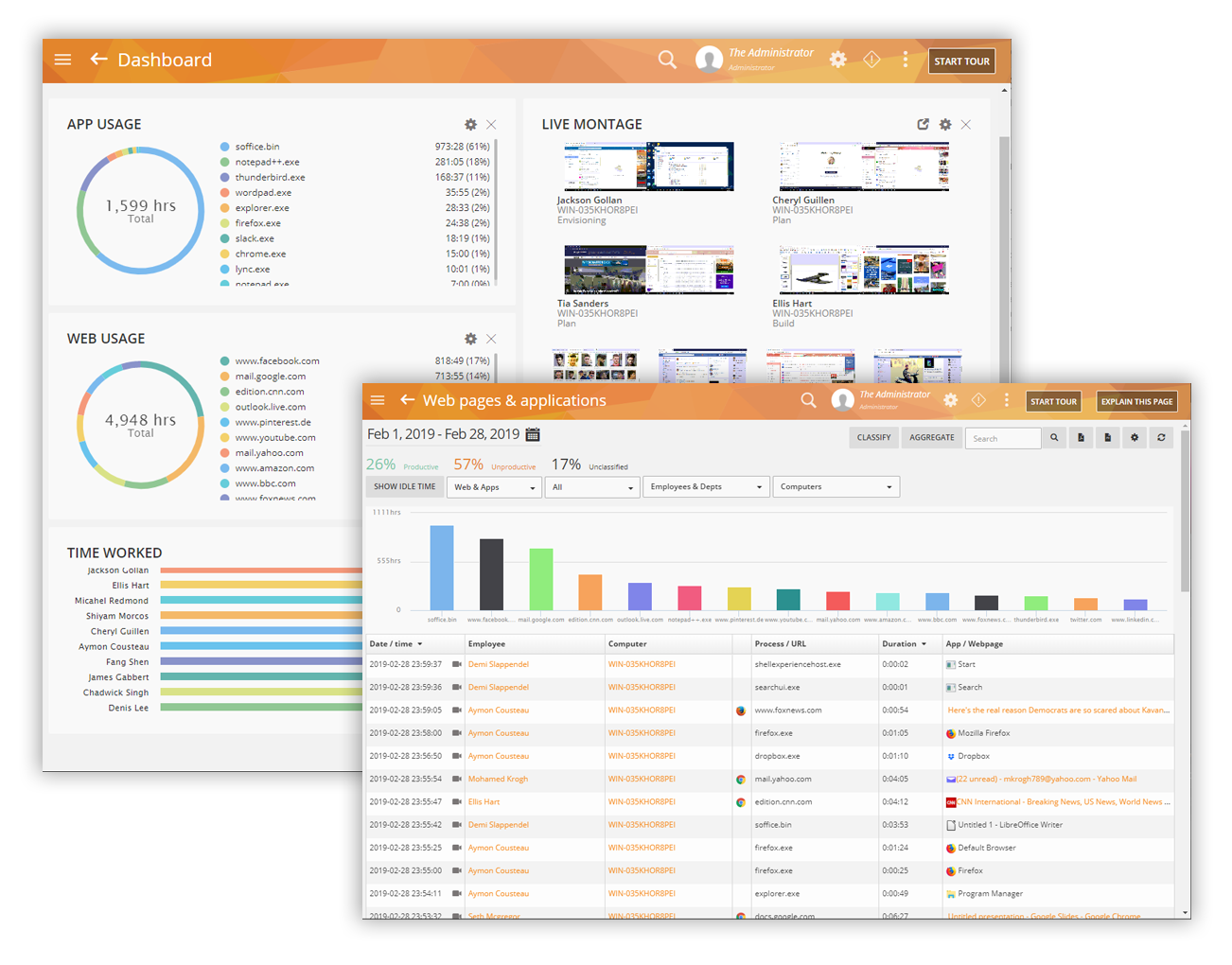
Monitor Activity in Real-Time

Employees spend the majority of their time on desktop using apps of websites. We use the TeraMind solution to allow clients to record and visualise every action in the case of a non-compliant action made against the business or negative efficiency. This can include desktop (screen), apps, websites, social media, instant messengers and more. Capture all the essential activity data like application/site name, URL, duration, etc. - This not only a powerful new solution that works, it's a solution that has increased productivity and awareness across the board.
Ensure Employee Privacy with Adjustable Tracking
Each monitored object like screen/apps/websites etc. can be configured to take into consideration what needs to be monitored and measured and who has access to the monitored records. You can control who you want to monitor, how much you want to monitor, when and for how long. This allows for instant administrative control to respect employee privacy requirements.
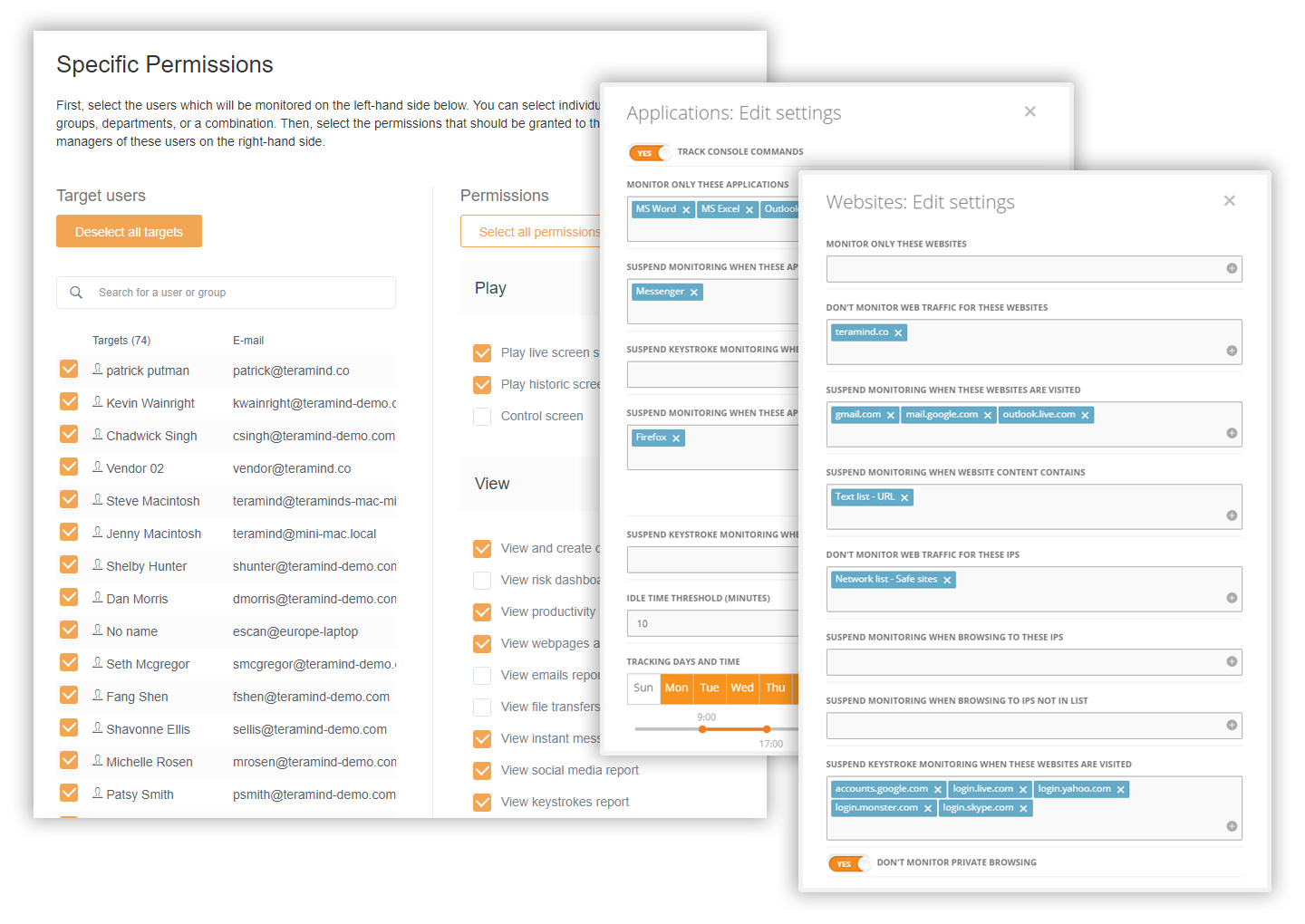

Detect Insider Threats with Intelligent Policy & Rules Engine
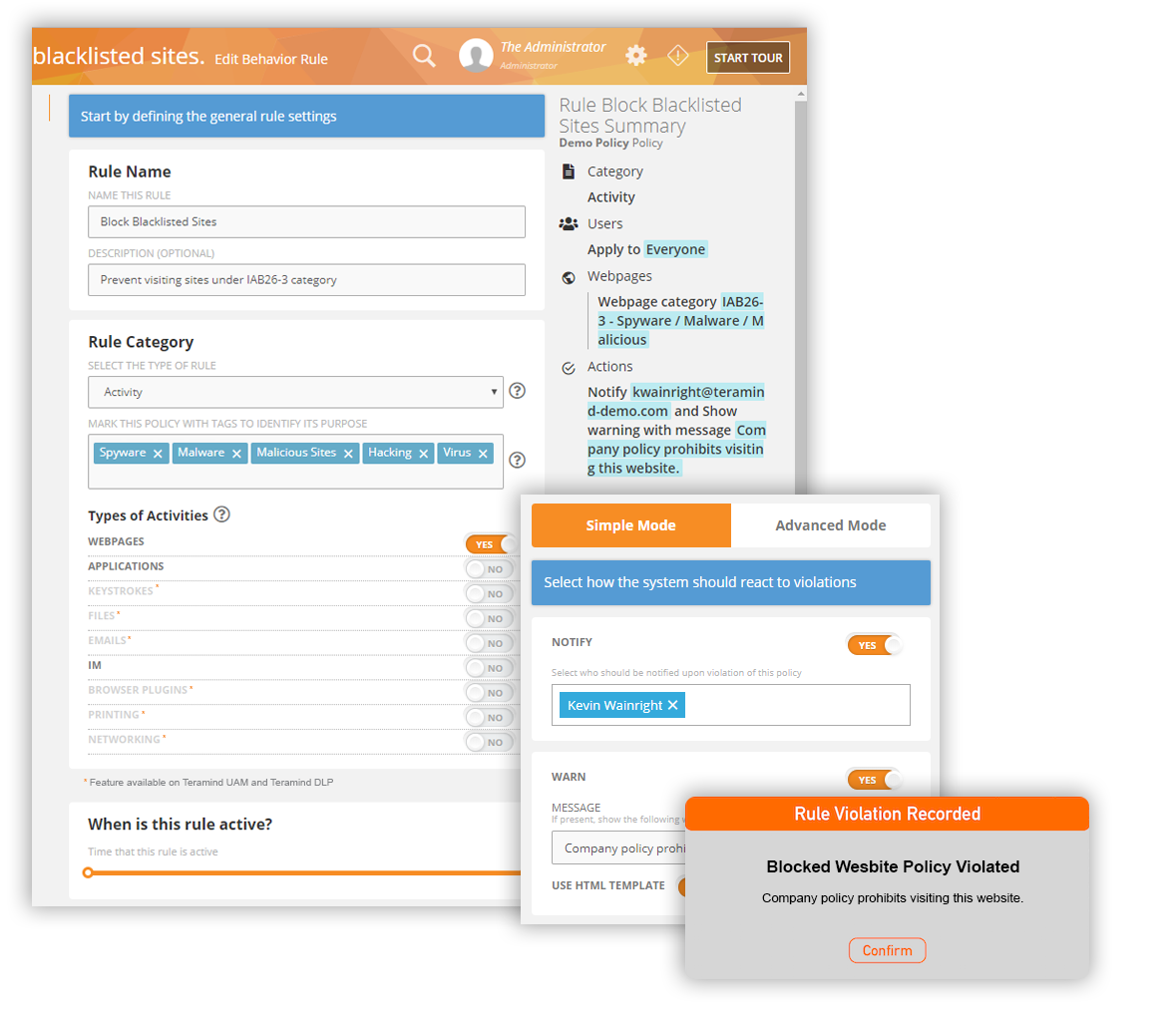
Determine what behaviours are high risk i.e. downloading files and attachments from an unknown website, running a risky application etc. Then, apply behaviour-based rules to detect when users violate the rules. The system will automatically block harmful employee activity or warn the user with a customised message about potential danger reducing false positives with minimal supervision. The system can also notify you about sensitive rule violation incidents that need your personal attention.
Boost Employee Productivity and Increase Organisational Performance
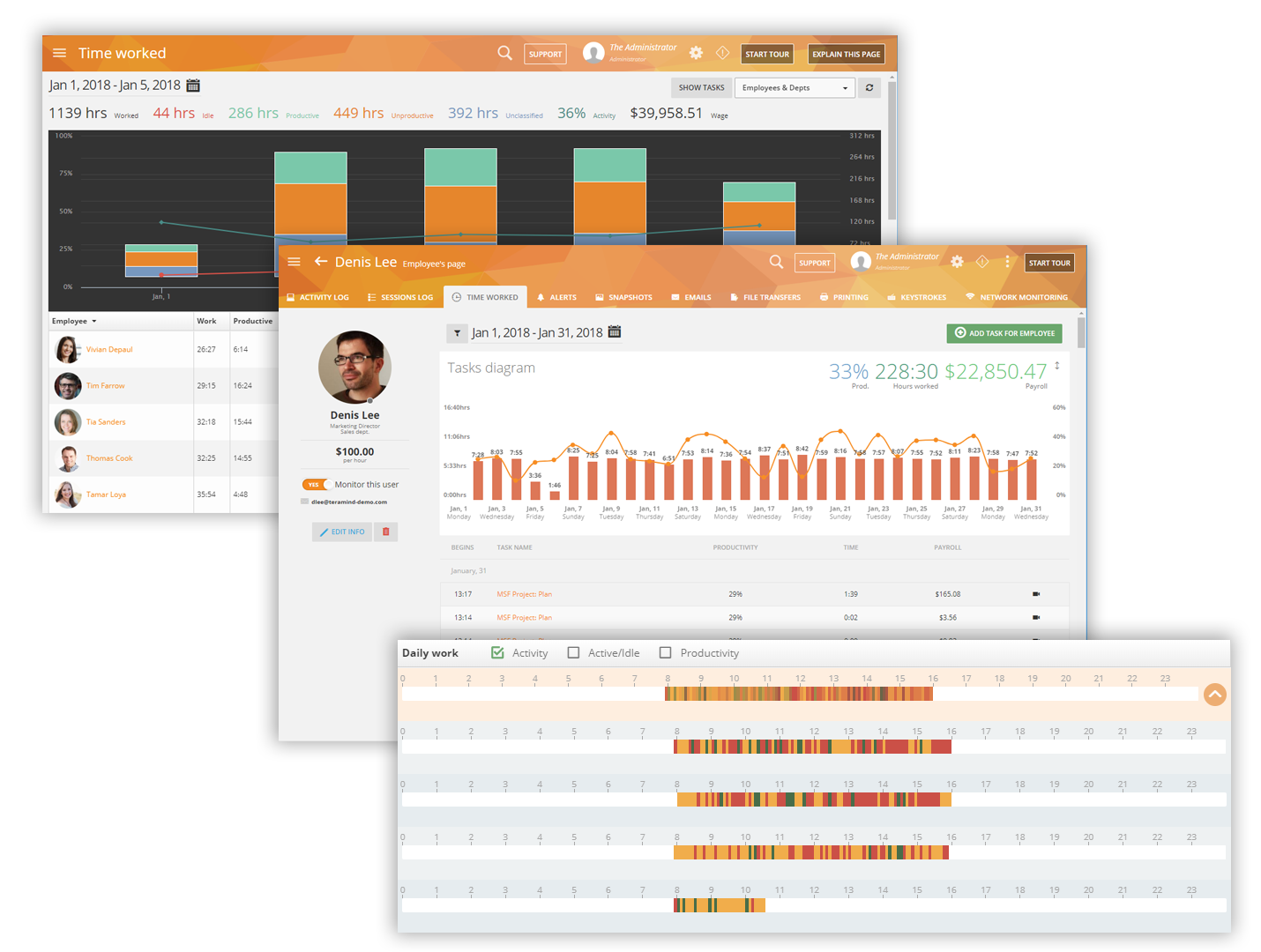
Use the workforce productivity tools to track active vs inactive time, late shifts, long breaks, etc. Use intelligent activity-based rules to automatically identify clues to customer dissatisfaction (angry sentiments in social media posts/customer query in instant messenger not answered etc.) and implement processes to provide better service.
Monitor Privileged Users for Extra Security
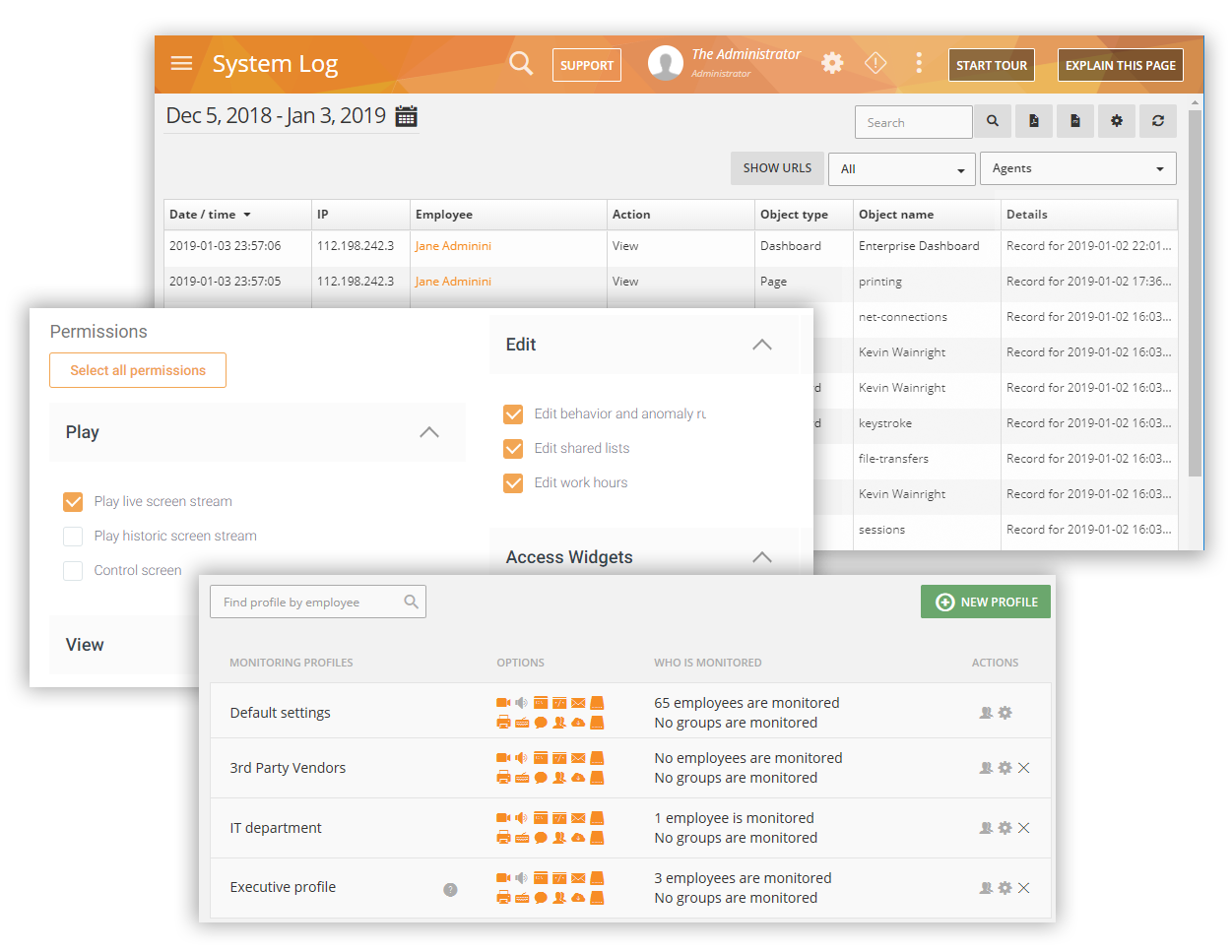
Teramind allows organisations to create profiles for remote and privileged employees and then define what information and system resources each profile can access. Create autonomous rules to notify the authorities of any suspicious privileged user activity, such as unscheduled login, access to system configuration, creation of backdoor accounts, etc.
Audit Security Incidents with Forensics
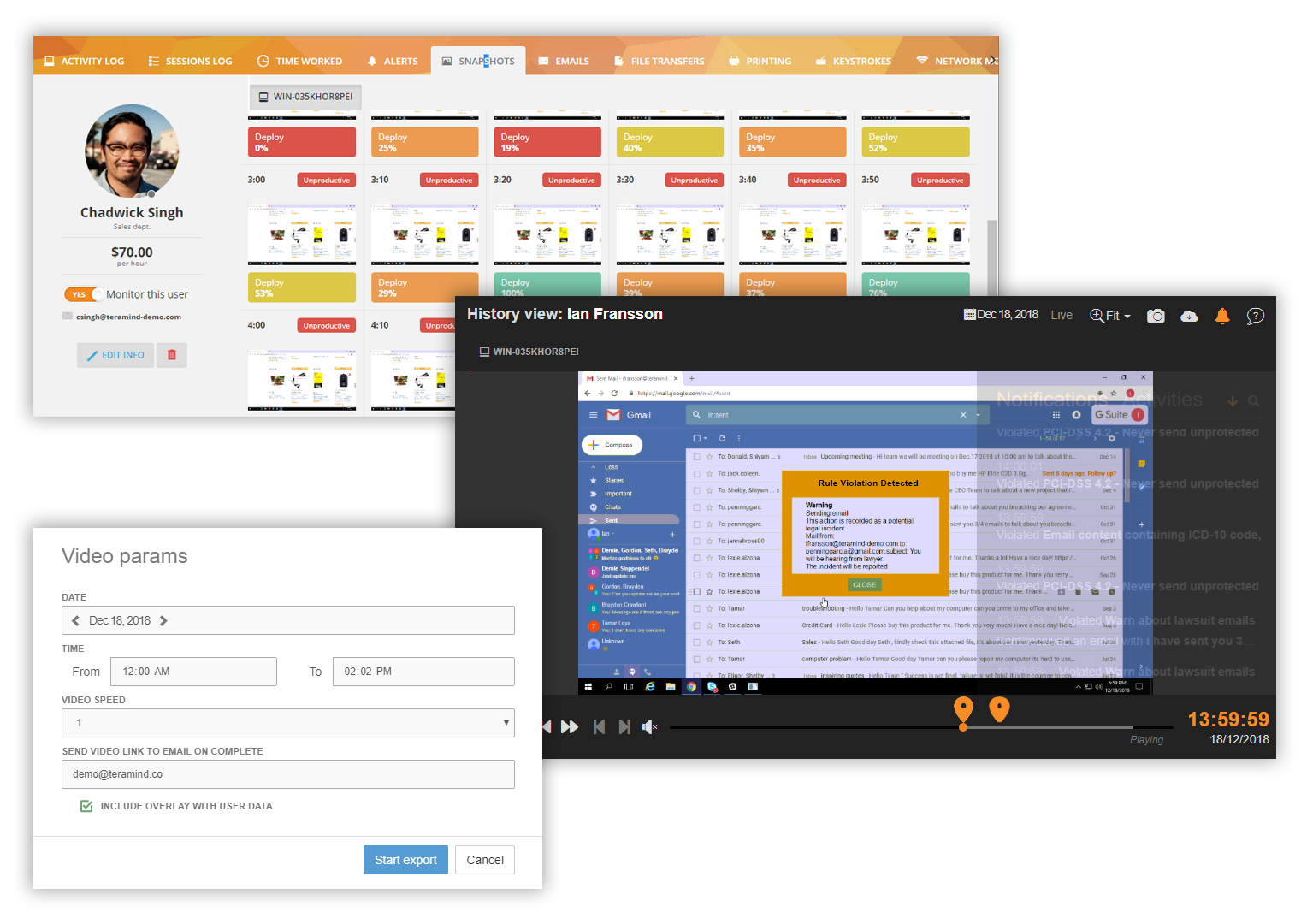
Detailed alerts for all users can be viewed including any security event and what action was taken, which app/site was involved, what data got accesses etc. Session recordings and history playback can be used to view user’s desktop or exported as MP4 video to be used as evidence in any investigation. Immutable system logs and session reports provide with further information to trace back to the source and cause of any security incident.
Talk to an expert
We'd love the opportunity to sit with you and discuss technology and your business