The ever growing Social Media landscape is the perfect location for hackers to send users to popular look-a-like websites such as ESPN, BBC News, Amazon and even Youtube to name a few. Once hackers have you in these locations and they have made users feel like it’s an authentic site, the most common modus operandi is a Chrome extension installation window which looks to spread malware.
Currently security researchers are continuously gaining warnings of a new malware campaign that has been active since (at least) last March, this year, and has already infected more than 100,000 users worldwide. This method of developing an identical site has been a strong and simple method of obtaining information from users that trust particular brands and is something that is not only a problem for the users but also companies that are losing brand loyalty every time an attack occurs, from big corporations to smaller entities.
The Malware which is dubbed ‘Nigelton’, is spreading rapidly through socially engineered links on facebook and infecting victims’ systems with maliciuos browser extensions that steal all of their social media credentials, installs cryptocurrency miners, and engages them in strong click fraud with an intentional outcome of obtaining credit card information.
“Radware has dubbed the malware “Nigelthorn” since the original Nigelify application replaces pictures to “Nigel Thornberry” and is responsible for a large portion of the observed infections.” reads the analysis published by Radware.
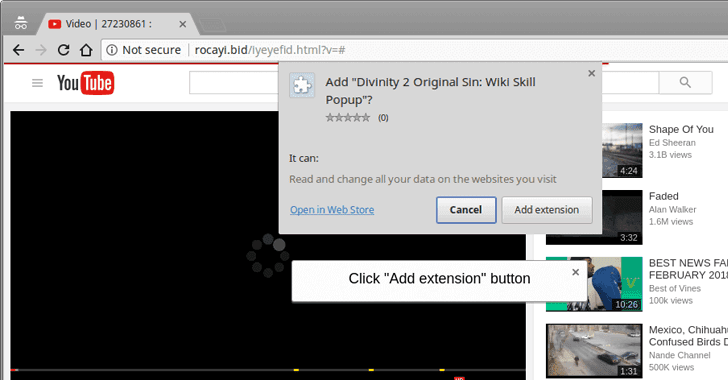
“The malware redirects victims to a fake YouTube page and asks the user to install a Chrome extension to play the video.”
According to a report published by Radware, te malware operators are using copies of legitimate Google Chrome extensions that looks tinject a shortm ofscated malicious script to start the malware operation. Radware believes that this is done to bypass Google’s extension validation checks.
The reason why this malware has been dubbed ‘Nigelthorn’ is because it was a copy of the popular ‘Nigelify’ extension which was designed to replace all pictures on a web page with gifs of ‘Nigel Thornberry’.
Nigelthorn Steals Passwords from Facebook/Instagram Accounts
Not only does the malware steal users passwords, if done via Facebook it can also collect personal details from your account. This stolen information is then used to send malicious links to friends of the infected person in an effort to push the same malicious extensions further. Which means that if any of those friends click on the shared link (that seems to come from the user), the whole infection process starts again but this time to the outer connections.
It’s reported that Nigelthorn also downloads a publicly available, browser-based cryptocurrency mining tool as a plugin to trigger the infected systems to start mining cryptocurrencies, including Monero, Bytecoin and Electroneum. Over the period of just 6 days, the attackers appeared to generate approximately $1,000 in cryptocurrencies, mostly obtained through the mining of Monero.
“The attackers are using a publicly available browser-mining tool to get the infected machines to start mining cryptocurrencies.” states Radware. “The JavaScript code is downloaded from external sites that the group controls and contains the mining pool. Radware observed that in the last several days the group was trying to mine three different coins (Monero, Bytecoin and Electroneum) that are all based on the “CryptoNight” algorithm that allows mining via any CPU.”
Trying to get out is tricky as the malicious code uses numerous techniques to gain persistence on the infected system, such as closing the extensions tab if the user attempts to access it, or downloading URI Regex from the C&C and blocking users from accessing Facebook and Chrome cleanup tools or from making edits, deleting posts, and posting comments.
The Malware
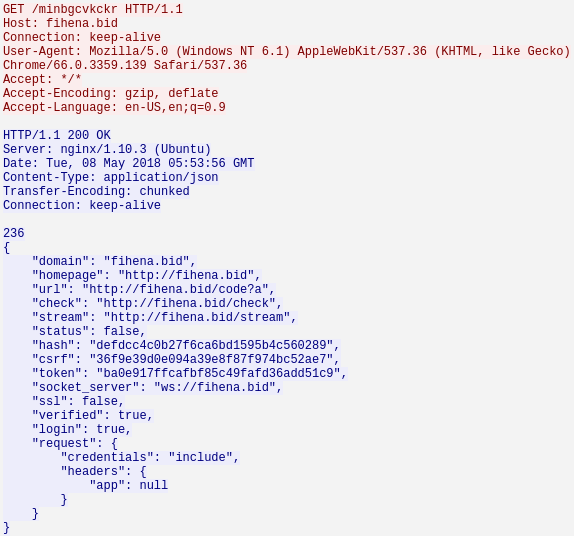
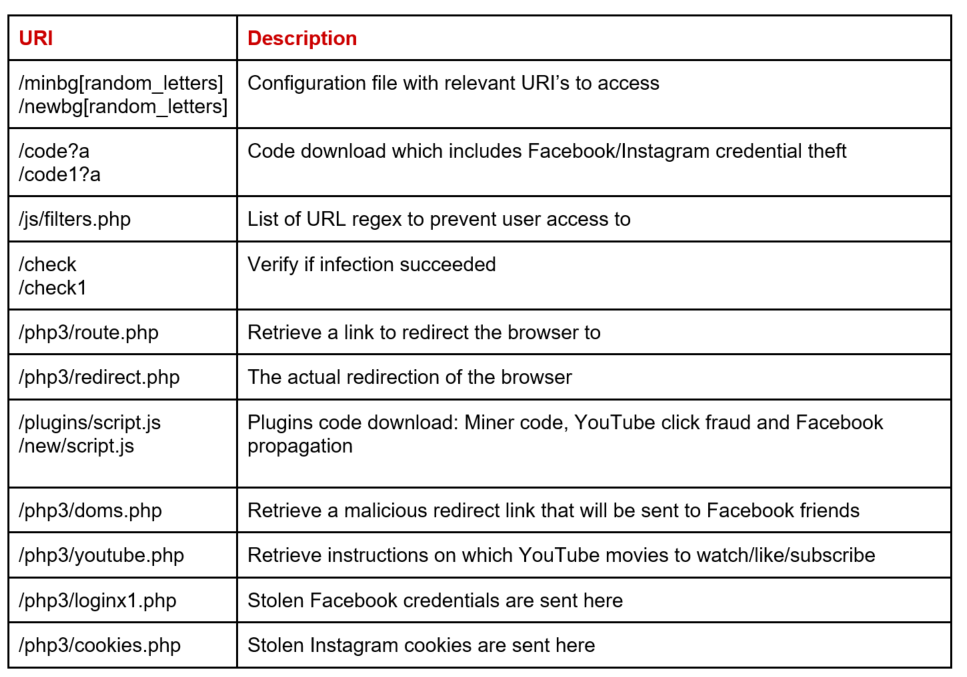
Once the the extension is installed on the users Chrome browser, it then generates a malicious JavaScript (seen above) that downloads the initial configuration form the C2. After the downloads are complete a set of requests is deployed, each with it’s own purpose and triggers. Here is the communication protocol released be Radware.
Known Extensions

If you like copying and pasting to find further information, here is a list of all seven extensions which are masquerading as legitimate Google extensions:
- Nigeligy
- PwnerLike
- Alt-j
- Fix-case
- Divinity 2 Original Sin: Wiki Skill Popup
- keeprivate
- iHabno
Although Google security has now removed all of the above-listed extensions, if you have previously installed these extensions across your Chrome browser, you are advised to immediately uninstall it and change passwords for your Facebook, Instagram as well as for other accounts where you have been using the same credentials. If you like spreading one password across every online platform, we suggest immediately accessing everything and making those changes right now!
As Facebook Spam Campaigns are quite common, users are advised to be vigilant when clicking on links and files which have been shared on the platforms even from family and friends.













Share your thoughts in the Comments section: